Of MAC Addresses and OUI: A Subtle, but Useful, Recon Resource
4.7
(536)
Write Review
More
$ 13.50
In stock
Description

Patch Tweak. Exploring Modular Synthesis (Kim Bjørn, Chris Meyer), PDF, Synthesizer

Hacking Exposed 2 - VoIP, PDF, Voice Over Ip
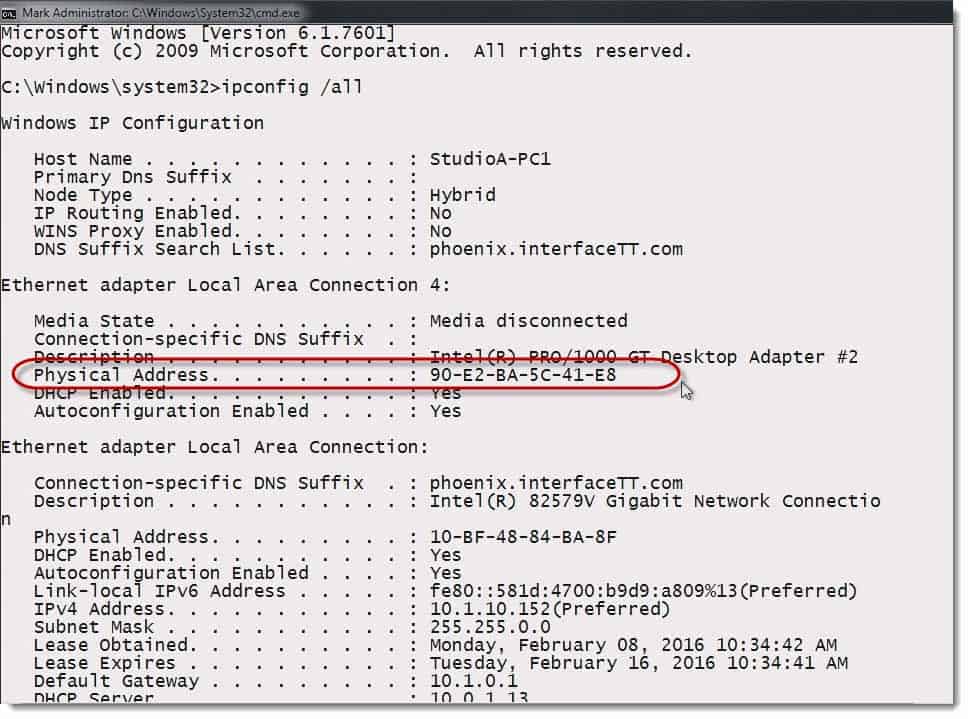
How MAC Addresses Are Assigned to Devices

Lesson 3 - Assessing Security Posture with Software Tools Flashcards

Our Branch International Courier Services In, 51% OFF

Kali Hacking Command
Professionally Evil Insights/Blogs
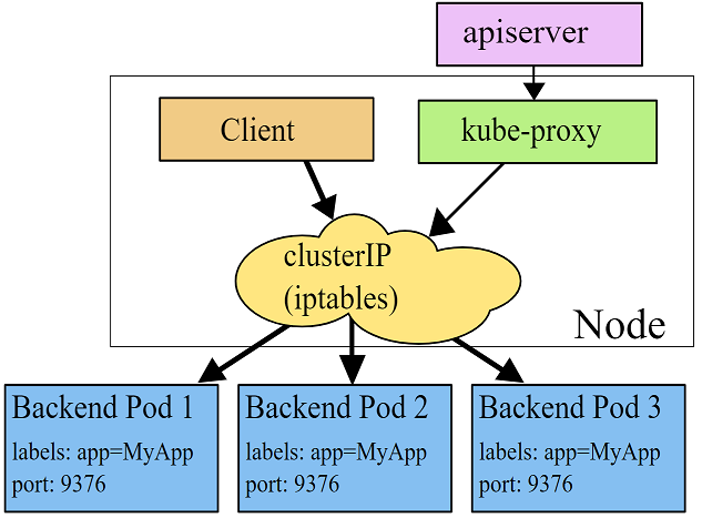
Attacking Kubernetes Clusters Through Your Network Plumbing: Part 1

Our Branch International Courier Services In, 51% OFF
Professionally Evil Insights/Blogs
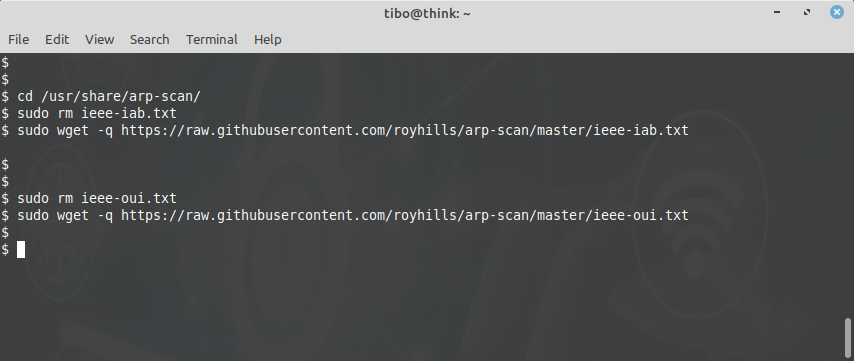
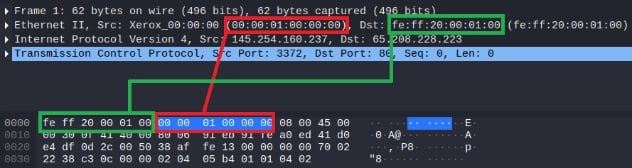
Network reconnaissance with arp-scan

MacLookup MAC Address Search
bitex/libs/coinkit/coinkit/words.py at master · blinktrade/bitex · GitHub
You may also like








